timeline
1900 BC: Hidden methods in Egyptian and early ciphers
100 BC: Caesar shift cipher used in Rome
9th c.: Al-Kindi invents frequency analysis
15th–16th c.: Polyalphabetic ciphers by Alberti and Vigenère
1883: Kerckhoffs defines key-based security
1940s: Enigma broken—math defeats secrecy
1949: Shannon formalizes cryptographic theory
1970s–2020s: Public-key and quantum-safe cryptography emerge
Cryptography Introduction
Section II: Cryptographic Primitives
Army Cyber Institute
April 9, 2026
Cryptography: From Obscurity to Mathematical Security
Cryptography shift from secrecy through obscurity to security through mathematics
What Is Cryptography?
Definition:
The study of mathematical techniques for securing information and proving authenticity in the presence of adversaries.
- Protects confidentiality, integrity, and authenticity.
- Provides non-repudiation.
- Operates at the heart of secure communication, digital signatures, and blockchain protocols.
- Enables trust in people to extend over untrusted channels through mathematics.
Why Cryptography Matters Today
- Our world depends on digital trust: banking, identity, communication, defense.
- Without cryptography, data could be altered, impersonated, or replayed at will.
- Cryptography enables trustless coordination—people can agree without knowing each other.
- The foundation of blockchain technology is cryptography.
From Secrecy to Integrity
| Early Goal | Modern Goal |
|---|---|
| Only confidentiality | Add message authenticity & integrity |
| Rely on secret methods | Rely on public algorithms + secret keys |
| Breakable by clever humans | Protected by computational infeasibility |
| Used for espionage & war | Used daily for commerce, identity, and confidentiality |
Mathematics — The Language of Trust
- Cryptography relies on formal logic and set theory to define security precisely.
- Symbols such as \(\in\) (“in”), \(\subseteq\) (“subset”), \(\Rightarrow\) (“implies”) express relationships among secrets, keys, and messages.
- \(\cap\) denotes intersection and indicates elements that are common between two sets.
- \(\cup\) denotes union and indicates the result of combining two sets together.
- A set is a collection of distinct elements.
- Example: \(K\) = {all possible keys}, \(M\) = {all possible messages}.
Sets and Functions
- Functions \(f : X \to Y\) map inputs to outputs (e.g., hash functions).
- A function \(f : X → Y\) maps each input to one output.
- A function is one-way if it’s easy to compute but hard to invert.
- Functions form the basis of hash algorithms, pseudo-random generators (PRG), and digital signatures.
Proofs and Reasoning
- Modern cryptography is based on proofs.
- Security properties are formal statements applying deductive reasoning to an initial premise.
- Proofs show that breaking a system would solve an already hard mathematical problem (e.g., factoring large primes).
- If the underlying problem is computationally prohibitive with modern computers, the scheme inherits security from that intractability.
Note that we say, “if.” These are assumptions, but quantum computers may prove these assumptions wrong.
Probability Refresher: Events and Outcomes
- Cryptography models uncertainty using probability spaces.
- Flip a fair coin → sample space \(\Omega = \{H, T\}\).
- Event \(E = \{H\}\); \(Pr(E) = \frac{1}{2}\).
- Flip a fair coin → sample space \(\Omega = \{H, T\}\).
- Randomness ensures unpredictability in keys and nonces.
- Security is often stated in terms of an adversary’s success probability.
More formally, proofs establish that no efficient adversary can gain advantage \(\epsilon >\) negligible over random guessing. The goal is that a ciphertext is indistinguishable from random noise.
Probability Refresher: Independence & Random Variables
- Independence: Two events \(A\) and \(B\) are independent if \(Pr(A \cap B) = Pr(A) × Pr(B)\).
- The outcome of one event does not impact the outcome of another: 2 coin flips.
- Random variable: a numeric outcome of a random process (\(X\) = result of a coin flip).
- Used to measure entropy (average unpredictability).
- Unpredictability, or randomness, is a crucial component to initialize modern crytopgraphic algorithms
What Is Randomness?
- True randomness: unpredictability with no discernible pattern.
- Deterministic systems (computers) can only simulate it.
- Randomness is essential for:
- Key generation
- Nonce and salt creation
- Proof-of-Work puzzles
- Key generation
- Weak randomness ⇒ predictable keys ⇒ broken security.
Aside: Human Randomness
Let’s try an exercise: choose a number between 1 and 100.
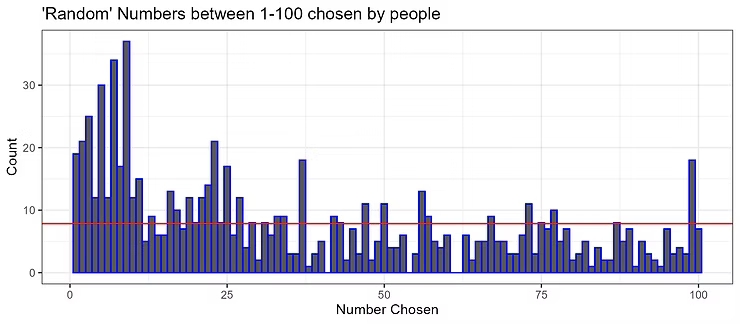
- Choosing more odd numbers than even numbers.
- Picking prime numbers more frequently.
- Avoiding multiples of 10, because they feel less “random.”
- Rarely choosing numbers like 1 and 100.
Sources of Randomness
- Physical entropy: radioactive decay, thermal noise, user input, network jitter.
- Algorithmic entropy: pseudorandom number generators (PRNGs) seeded by physical sources.
- Hybrid systems: hardware RNG → seed → software PRG.
- Security depends on entropy quality — if attackers predict the seed, all outputs are compromised.
- Blockchain systems rely on secure randomness for mining, validator selection, and nonce generation.
Pseudorandom Generators (PRGs)
- A pseudorandom generator (PRG) stretches a short, truly random seed into a long sequence that appears random.
- Formally: \(G : \{0,1\}^{n} \to \{0,1\}^{m}\), where \(m \gg n\).
- The output is computationally indistinguishable from true randomness.
- Enables practical cryptography without needing infinite entropy sources.
Desirable Properties of PRGs
- Efficiency: \(G\) must run in polynomial time (vs. exponential time)
- Expansion: Output length \(m\) must be significantly larger than seed length \(n\).
- Unpredictability: Given the output \([1..k]\) of \(G(s)\), it should be infeasible to predict \([k+1]\).
- Indistinguishability: No efficient algorithm can distinguish PRG output from true randomness.
- Reproducibility: The same seed always generates the same sequence (important for testing and simulation).
When Random Goes Wrong
- Weak or repeated randomness has broken real systems:
- Android Bitcoin Wallet (2013): repeated nonces allowed key recovery.
- Debian OpenSSL Bug (2008): flawed entropy reduced key space to \(2^{15}\) possibilities.
- Sony PlayStation 3 (2010): reused signature nonces exposed private keys.
- Android Bitcoin Wallet (2013): repeated nonces allowed key recovery.
Computational Hardness
- Cryptographic security depends on computational hardness — problems so difficult that no efficient algorithm can solve them.
- Factoring: given \(N = p × q\), find \(p\) and \(q\).
- Factoring: given \(N = p × q\), find \(p\) and \(q\).
- In practice, “hard” means no known algorithm can solve it in polynomial time.
Cryptography and Trustless Systems
- Traditional trust model: rely on central authority (bank, government)
- Trustless model: replaces central authority with mathematical proof.
- Result: security and agreement without mutual trust.
- Trustless model is foundation for blockchain technology.
How Blockchain Uses Cryptography
- Hash functions ensure data integrity — every block depends on the hash of the previous one.
- Pseudorandomness introduces fairness and unpredictability (e.g., mining puzzles, validator selection).
- Digital signatures verify transaction authenticity.
- Consensus protocols use cryptographic proofs to coordinate nodes without trust.
- Together, they enable a tamper-evident, decentralized ledger.
Example: The Double-Spend Problem
- One key challenge for digital money: prevent one coin from being spent twice.
- Without a central ledger, how do you ensure all copies of data stay consistent?
- Blockchain solves this using:
- Cryptographic hashing to link blocks.
- Timestamped consensus to order transactions.
- Proof-of-Work / Proof-of-Stake to make rewriting history infeasible.
- Cryptographic hashing to link blocks.
- Cryptography ensures tamper-evidence and global agreement.
Summary
- Cryptography evolved from secret writing to mathematical assurance.
- Randomness and pseudorandomness underpin all digital security.
- Computational hardness makes attacks infeasible.
- Blockchain depends on these principles to replace trust with verification.
References
[1]
J. Katz and Y. Lindell, Introduction to Modern Cryptography, 3rd ed. Chapman and Hall/CRC, 2020. doi: 10.1201/9781351133036.
[2]
O. Goldreich, “The Foundations of Cryptography.” May 2004. Accessed: Oct. 23, 2025. [Online]. Available: https://www.wisdom.weizmann.ac.il/~oded/foc-book.html
[3]
D. Eastlake, J. Schiller, and S. Crocker, RFC 4086: Randomness Requirements for Security. The Internet Society, 2005. Accessed: Oct. 23, 2025. [Online]. Available: https://datatracker.ietf.org/doc/html/rfc4086
[4]
E. B. Barker and J. M. Kelsey, “Recommendation for random number generation using deterministic random bit generators,” National Institute of Standards and Technology, Gaithersburg, MD, NIST SP 800-90a, 2012. doi: 10.6028/NIST.SP.800-90a.
[5]
J. Bonneau, J. Clark, and S. Goldfeder, “On Bitcoin as a public randomness source.” Cryptology ePrint Archive, Paper 2015/1015, 2015. Available: https://eprint.iacr.org/2015/1015
[6]
M. Blum and S. Micali, “How to Generate Cryptographically Strong Sequences of Pseudorandom Bits,” SIAM J. Comput., vol. 13, no. 4, pp. 850–864, Nov. 1984, doi: 10.1137/0213053.
[7]
M. Bellare and P. Rogaway, “Introduction to Modern Cryptography.” Nov. 05, 2005. Available: https://web.cs.ucdavis.edu/~rogaway/classes/227/spring05/book/main.pdf
[8]
F. Weimer, “[SECURITY] [DSA 1571-1] New openssl packages fix predictable random number generator.” [Online]. Available: https://lists.debian.org/debian-security-announce/2008/msg00152.html
[9]
N. Heninger, Z. Durumeric, E. Wustrow, and J. A. Halderman, “Mining your ps and qs: Detection of widespread weak keys in network devices,” in 21st USENIX security symposium (USENIX security 12), Bellevue, WA: USENIX Association, Aug. 2012, pp. 205–220. Available: https://www.usenix.org/conference/usenixsecurity12/technical-sessions/presentation/heninger
[10]
W. Diffie and M. Hellman, “New Directions in Cryptography,” in IEEE Transactions on Information Theory, 1976, pp. 644–654. doi: 10.1109/TIT.1976.1055638.
[11]
R. L. Rivest, A. Shamir, and L. Adleman, “A method for obtaining digital signatures and public-key cryptosystems,” Commun. ACM, vol. 21, no. 2, pp. 120–126, Feb. 1978, doi: 10.1145/359340.359342.
[12]
S. Nakamoto, “Bitcoin: A Peer-to-Peer Electronic Cash System.” Satoshi Nakamoto Institute, Oct. 31, 2008. Accessed: Sep. 12, 2025. [Online]. Available: https://cdn.nakamotoinstitute.org/docs/bitcoin.pdf
[13]
A. Narayanan, J. Bonneau, E. Felten, A. Miller, and S. Goldfeder, Bitcoin and Cryptocurrency Technologies. Princeton University Press, 2016.
[14]
J. Bonneau, A. Miller, J. Clark, A. Narayanan, J. A. Kroll, and E. W. Felten, “SoK: Research Perspectives and Challenges for Bitcoin and Cryptocurrencies,” in 2015 IEEE Symposium on Security and Privacy, 2015, pp. 104–121. doi: 10.1109/SP.2015.14.

Cryptography Introduction — Army Cyber Institute — April 9, 2026