Symmetric Encryption
Section II: Cryptographic Primitives
April 9, 2026
The Shared Key
- Imagine two field agents need to communicate. They share one identical key that locks and unlocks the same safe.
- They exchange messages by visiting the safe and depositing and retrieving notes.
- This is the essence of symmetric cryptography: one shared secret for both encryption and decryption.
- Contrast with hashing: Hashes are one-way commitments; symmetric ciphers are reversible with the key.
Exclusive OR (XOR) Logic
- Definition: XOR outputs
1if exactly one of its inputs is1; otherwise0.- Denoted by symbols:
⊕,^, or sometimesXOR.
- Common in cryptography, checksums, and parity bits.
- Denoted by symbols:
Truth Table:
| A | B | A ⊕ B |
|---|---|---|
| 0 | 0 | 0 |
| 0 | 1 | 1 |
| 1 | 0 | 1 |
| 1 | 1 | 0 |
Properties:
- Commutative:
A ⊕ B = B ⊕ A
- Associative:
(A ⊕ B) ⊕ C = A ⊕ (B ⊕ C)
- Identity:
A ⊕ 0 = A
- Self-inverse:
A ⊕ A = 0
Visualization: Think of a “difference detector” — it lights up when inputs differ.
Infinite-length One Time Pad
Imagine you and a friend share a secret, infinite-length pad of random text
Could establish perfect secrecy if you never reused the same offset into pad
- Encrypt: msg \(\oplus\) pad-at-offset \(\to\) ciphertext
- Decrypt: ciphertext \(\oplus\) pad-at-offset \(\to\) plaintext
- Share: (ciphertext, offset)
Test XOR with a OTP here: XOR Pad Demo
Pseudo-Random Generators
- Infinite-length, pre-shared keys do not exist, but let’s assume PRGs do
- A psuedo-random number generator generates a stream of text
- You preshare a random seed for the generator, and then follow same algorithm in previous slide
- Essentially a very primitive stream cipher
- Weakness:
- No error correction
- Must track offset
Simple Pseudorandom Generator
Let \(h\) be a cryptographic hash function
\(h : \{0,1\}^* \to \{0,1\}^n\)Let the initial seed be \(s_0 \in \{0,1\}^n\)
For each round \(i = 1, 2, \dots, t\):
- Compute \(h_i = h(s_{i-1})\)
- Output the last byte of \(h_i\):
\(y_i = \mathrm{LSB}_8(h_i)\)
- Use the remaining bits of \(h_i\) as the next seed:
\(s_i = h_i[0 : n - 8]\)
- Compute \(h_i = h(s_{i-1})\)
Final output: \(y_1 \,\|\, y_2 \,\|\, \dots \,\|\, y_t\)
Visualize this: PRG Demo
Interpretation: Each iteration hashes the current seed, emits one byte as pseudorandom output, and reuses the rest as the next seed. However, this structure is not provably secure.
Counter-Mode Pseudorandom Generator (PRG)
- Let \(F\) be a pseudorandom function (PRF) keyed by a secret key (e.g., \(F_K(x)=\mathrm{HMAC}_h(K,x)\)).
- Let the seed be the secret key \(K \in \{0,1\}^k\) and initialize a counter \(ctr_1 \in \{0,1\}^c\).
- \(F : \{0,1\}^k \times \{0,1\}^c \to \{0,1\}^n\)
- For each round \(i = 1,2,\dots,t\):
- Compute a block with the PRF:
\(B_i \;=\; F_K(ctr_i)\) - Output (e.g., the last byte):
\(y_i \;=\; \mathrm{LSB}_8(B_i)\) - Increment the counter:
\(ctr_{i+1} \;=\; ctr_i + 1 \pmod{2^c}\)
- Compute a block with the PRF:
- Final output: \(y_1 \,\|\, y_2 \,\|\, \dots \,\|\, y_t\)
Interpretation: Use a secret key \(K\) and a public counter to “seek” through a PRF. Each \(B_i\) is pseudorandom; selecting a byte (or more) per round yields a secure keystream.
What Is Symmetric Cryptography?
- Definition: Encryption and decryption using the same secret key.
- Mathematical form:
- Encryption Eₖ(plaintext) = ciphertext
- Decryption Dₖ(ciphertext) = plaintext
- Where Dₖ(Eₖ(m)) = m
- Encryption Eₖ(plaintext) = ciphertext
- Examples: AES, ChaCha20, DES (legacy).
- Fast and efficient—used for bulk data, VPNs, and storage encryption.
Shannon’s Principles: Confusion and Diffusion
| Principle | Purpose | Example |
|---|---|---|
| Confusion | Obscure the relationship between key and ciphertext. | Substitution tables (S-boxes) |
| Diffusion | Spread the influence of each plaintext bit across many ciphertext bits. | Permutation layers (P-boxes) |
- Introduced by Claude Shannon (1949).
- Together, they create complex, unpredictable ciphertext from simple transformations.
Building Blocks of Block Ciphers
- Block ciphers process fixed-size chunks (e.g., 128 bits).
- Built from repeated rounds combining:
- Substitution (S-box): non-linear mapping for confusion.
- Permutation (P-box): bit re-ordering for diffusion.
- Key mixing: XOR with a round key derived from the main key.
- Substitution (S-box): non-linear mapping for confusion.
- Multiple rounds amplify security—small changes in plaintext or key cause large changes in ciphertext.
Block vs Stream Ciphers
| Feature | Block Cipher | Stream Cipher |
|---|---|---|
| Unit of operation | Fixed-size blocks (e.g., 128 bits) | Single bits or bytes |
| Key use | Same key for many rounds | Key generates continuous keystream |
| Examples | AES, DES | ChaCha20, RC4 |
| Strength | Strong diffusion and structure | High speed and low latency |
| Typical use | Disk, file encryption | Real-time communication, VPNs |
Modes of Operation Visual

Photo Credit: A.M. Rowsell and Epachamo, CC-BY-SA 4.0. Wikipedia
Modes of Operation Overview
| Mode | Description | Strengths | Weaknesses |
|---|---|---|---|
| ECB | Encrypts each block independently. | Simple, parallelizable. | Reveals patterns (insecure). |
| CBC | Chains each block to the previous via XOR with IV. | Hides patterns, strong diffusion. | Sequential; needs IV. |
| CFB | Turns block cipher into self-synchronizing stream. | Handles short data streams. | Bit errors propagate. |
| CTR | Encrypts counter values to generate keystream. | Parallelizable, random access. | Requires unique nonce. |
ECB Mode Pitfall
- Electronic Codebook (ECB) encrypts each block independently.
- Identical plaintext blocks → identical ciphertext blocks.
- Leaks patterns in structured data (images, database fields).
- Never use ECB for real-world encryption.
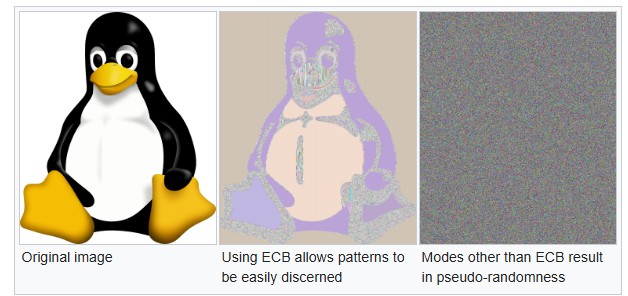
Photo Credit: Larry Ewing. Wikipedia
Padding and Initialization Vectors
- Padding: ensures plaintext fits exact block size (e.g., PKCS#7).
- Example: “HELLO” →
HELLO\x03\x03\x03for 8-byte block.
- Example: “HELLO” →
- Initialization Vector (IV): random, unique value prepended or sent alongside ciphertext.
- Ensures identical plaintexts encrypt differently each time.
- Ensures identical plaintexts encrypt differently each time.
- Padding adds length consistency; IVs add semantic security (freshness).
- IVs are not secret but must be unpredictable and never reused.
From Confidentiality to Authenticated Encryption (AEAD)
Confidentiality hides contents; integrity detects tampering; authenticity binds to a key holder.
AEAD schemes provide both confidentiality and integrity in one API.
- Authenticated Encryption with Associated Data (AEAD)
Associated Data (AAD): authenticated but unencrypted headers/metadata.
Examples: AES-GCM, ChaCha20-Poly1305; older pattern: Encrypt-then-MAC with HMAC.
Why Symmetric Crypto
- Speed: Thousands of times faster than public-key/asymmetric encryption.
- Security: AES and ChaCha20 remain unbroken with proper key management.
- Ubiquity: Protects VPNs, Wi-Fi (WPA3), TLS session data, and encrypted drives.
- Limitation: Requires secure key distribution and rotation.
- Block Ciphers provide conceptual frame of reference block chaining.
- Blockchains are like CBC in that they computation cannot be parallelized.
Symmetric Crypto Micro Lab
References

Symmetric Encryption — Army Cyber Institute — April 9, 2026